I thought there was a need for a cellular blockchain variant, and a more sustainable alternative to cryptocurrencies like Bitcoin that depend on unsustainable proofs-of-work. So I designed one and gave it a temporary project name of Grapevine. I like biomimetics, which I used for both the blockchain itself and its derivative management/application/currency/SW distribution layer. The ANTs were my invention in 1993 when I was with BT, along with Chris Winter. BT never did anything with it, and I believe MIT later published some notes on the idea too. ANTs provide an ideal companion to blockchain and together, could be the basis of some very secure IT systems.
The following has not been thoroughly checked so may contain serious flaws, but hopefully contain some useful ideas to push the field a little in the right direction.
A cellular, distributed, secure ledger and value assurance system – a cheap, fast, sustainable blockchain variant
- Global blockchain grows quickly to enormous size because all transactions are recorded in single chain – e.g. bitcoin blockchain is already >100GB
- Grapevine (temp project name) cellular approach would keep local blocks small and self-contained but assured by blockchain-style verification during growth and protected from tampering after block is sealed and stripped by threading with a global thread
- Somewhat analogous to a grape vine. Think of each local block as a grape that grow in bunches. Vine links bunches together but grapes are all self-contained and stay small in size. Genetics/nutrients/materials/processes all common to entire vine.
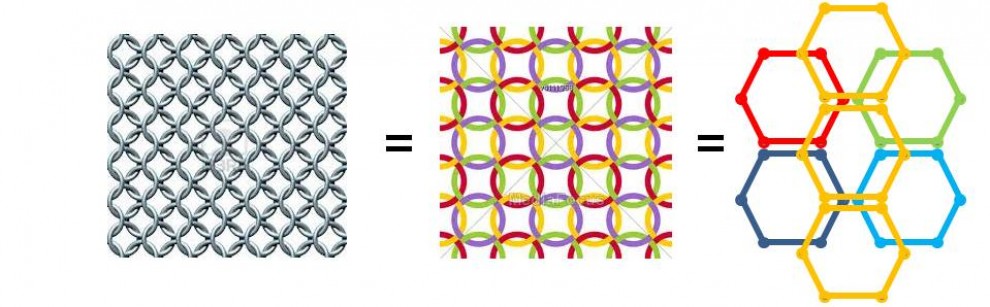
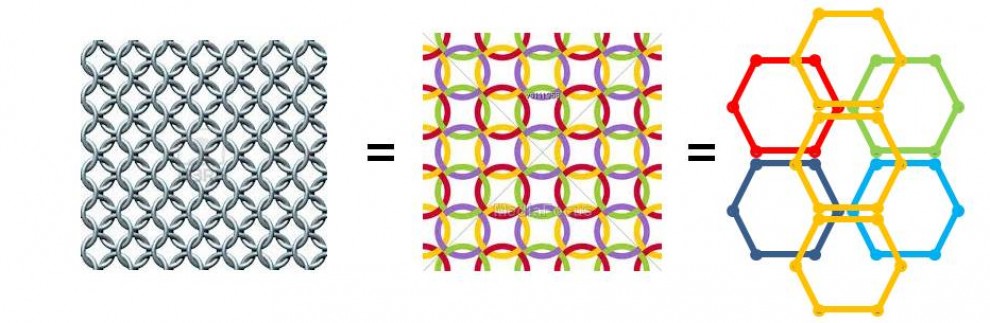
- Grape starts as a flower, a small collection of unverified transactions. All stamens listen to transactions broadcast via any stamen. Flower is periodically (every minute) frozen (for 2 seconds) while pollen is emitted by each stamen, containing stamen signature, previous status verification and new transactions list. Stamens check the pollen they receive for origin signature and previous growth verification and then check all new transactions. If valid, they emit a signed pollination announcement. When each stamen has received signed pollination announcements from the majority of other stamens, that growth stage is closed, (all quite blockchain-like so far), stripped of unnecessary packaging such as previous hash, signatures etc) to leave a clean record of validated transactions, which is then secured from tampering by the grape signature and hash. The next stage of growth then begins, which needs another pollination process (deviating from biological analogy here). Each grape on the bunch grows like this throughout the day. When the grapes are all fully grown, and the final checks made by each grape, the grapes are stripped again and the whole bunch is signed onto the vine using a highly secure bunch signature and hash to prevent any later tampering. Grapes are therefore collections of verified local transactions that have grown in many fully verified stages during the day but are limited in size and stripped of unnecessary packaging. The bunch is a verified global record of all of the grapes grown that day that remains the same forever. The vine is a growing collection of bunches of grapes, but each new grape and bunch starts off fresh each day so signalling and the chain never grow significantly. Each transaction remains verified and recorded forever but signalling is kept minimal. As processing power increases, earlier bunches can be re-secured using a new bunch signature.
Key Advantages
- Grape vine analogy is easier for non-IT managers to understand than normal blockchain.
- Unlike conventional blockchains, blocks grow in stages so transactions don’t have to wait long to be verified and sealed.
- Cellular structure means signalling is always light, with just a few nearby nodes checking a few transactions and keeping short records.
- Ditto bunching, each day’s records start from zero and bunch is finished and locked at end of day.
- Cellular structure allows sojourn time for signalling to be kept low with potentially low periods for verification and checking. Will scale well with improving processing speed, less limited by signal propagation time than non-cellular chains.
- Global all-time record is still complete, duplicated, distributed, but signalling for new transactions always starts light and local every new day.
- Cellular approach allows easy re-use of globally authenticated tokens within each cell. This limits cost of token production.
- Cells may be either geographic or logical/virtual. Virtual cells can be geographically global (at penalty of slower comms), but since each is independent until the end of the day, virtual cell speed will not affect local cell speed.
- Protocols can be different for different cells, allowing cells with higher value transactions to use tighter security.
Associated mechanisms
- Inter-cell transactions can be implemented easily by using logical/virtual cell that includes both parties. Users may need to be registered for access to multiple cells. If value is being transferred, it is easy to arrange clearing of local cell first (1 minute overhead) and then check currency hasn’t already been spent before allowing transaction on another cell.
- Grapes are self-contained and data is held locally, duplicated among several stamens. Once sealed for the day, the grape data remains in place, signed off with the appropriate grape signature and the bunch signature verifies it with an extra lock that prevents even a future local majority from being able to tamper with it later. To preserve data in the very long-term against O/S changes, company failure etc, subsequent certified copies may be distributed and kept updated.
- Signalling during the day can be based on ANT (autonomous network telepher) protocols. These use a strictly limited variety of ANT species that are authenticated and shared at the start of a period (a day or a week perhaps), using period lifetime encryption keys. Level of encryption is determined by ensuring that period is much smaller than the estimated time to crack on current hardware at reasonable cost. All messages use this encryption and ANT mechanisms therefore chances of infiltration or fraudulent transaction is very low so associated signalling and time overhead costs are kept low.
- ANTs may include transaction descriptor packets, signature distribution packets, new key distribution packets, active (executable code) packets, new member verification packets, software distribution, other admin data, performance maintenance packets such as load distribution, RPCs and many others. Overall, perhaps 64 possible ANT species may be allowed at any one time. This facility makes the system ideal for secure OS and software distribution/maintenance.
Financial use
- ANTs can contain currency to make valuable packets, or an ANT variant could actually be currency.
- Optional coins could be made for privacy, otherwise transactions would use real world accounts. A coin-based system can be implemented simply by using the grape signature and coin number. Coins could be faked by decrypting the signature but that signature only lasts one period so by then they will be invalid. Remember, encryption level is set according to cost to decrypt during a period. Coins are globally unique due to different cells having different signatures. Once grapes are sealed no tampering is possible.
- One mechanism is that coins are used as temporary currency that only lasts one period. Coins are bought using any currency immediately before transactions. At end of day, coins are converted back to desired currency. Any profits/losses due to conversion differences during day accrue to user at point of conversion.
- A lingering cybercurrency can be made that renews its value to live longer than one period. It simply needs conversion to a new coin at the start of the new day, relying on signature security and short longevity to protect.
- ANTs can alternatively carry real currency value by direct connection to any account. At end of each growth stage or end of day, transaction clearing debits and deposits in each respective account accordingly.
- Transaction fees can be implemented easily and simply debited at either or both ends.
- No expensive PoW is needed. Wasteful mining and PoW activity is unnecessary. Entire system relies only on using encryption signatures that are valid for shorter times than their cost-effective decryption times. Tamper-resistance avoids decryption of earlier signatures being useful.
With thanks to my good friend Prof Nick Colosimo for letting me bounce the ideas off him.